(How-To) Replace NSX-T Self-Signed Certificates
Once you have completed the install of your three NSX-T manager nodes it is a good idea to replace the certificates with certificate authority (CA) signed certificates with your domain. This will provide better security knowing the web page you are connecting to is trusted. Also, you can avoid that annoying “Your connection is not private” page. We will walk through how to replace all the system generated certificates used with the NSX-T manager platform.
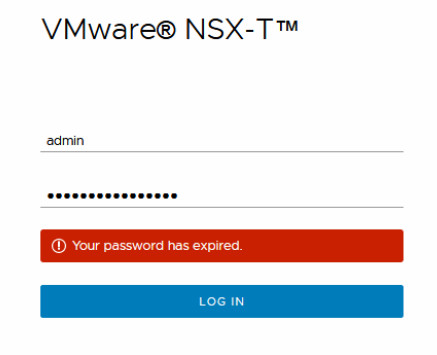
(Troubleshooting) NSX-T Manager Disk is Full
If the NSX-T manager appliance disk gets full, the manager may not function properly. The appliance can be sluggish or unresponsive. Logins can fail even though you KNOW the password you are entering is correct. We will walk through how to recover your NSX-T manager appliance by freeing up disk space when you cannot login due to the disk being full.
(How-To) Reset/Recover NSX-T Root Password
We’ve all heard about or been in the position where the only person who knew a critical server password has left the company. Or over time and through various change control, the password documented is no longer working and rebuilding the server from scratch for any reason is never appealing, let alone the core appliance […]
Read More »
(How-To) Install Your First NSX-T Manager Node
We walk through how to deploy the OVF of the NSX-T manager using the OVF wizard from within vCenter server.
(How-To) Disable NSX-T Manager TLS Protocol Versions
To ensure our servers are only accepting connections using secure cryptographic protocols we often need to restrict which protocols are enabled on a server. NSX-T manager appliances include TLSv1.1 and TLSv1.2 enabled by default. This article will walk you through confirming what TLS protocols are enabled as well as how to disable TLS protocol versions to harden your deployment.
(How-To) Setup Automatic Backups For NSX-T
We are going to walk through how to successfully configure automatic SFTP backups of our NSX-T manager as well as walk through the folder structure created during each backup and what log messages are generated so you can spot key phases of the backup being passed so you can narrow your troubleshooting if a backup failure occurs. Finally, we will walk through how to automate the cleanup of old backup files.
(How-To) Setup an OpenSSH SFTP Server to Store NSX-T Backups
We are going to walk through configuring an Ubuntu 18.04 LTS server with a dedicated service account to be used for backing up your NSX-T appliances.
(How-To) Configure NSX-T Uplink Profiles
An Uplink Profile defines how an N-VDS residing on a respective transport node will map to the physical NICs of a host. The configurable properties of an uplink profile determines how transport nodes connect to the physical network by configuring the number of NICs, teaming policies, VLANs and MTU.
The benefit of creating a custom uplink policy allows you to configure the desired state once and enforce that desired state everywhere. Thus, creating a consistent and reliable deployment.
(How-To) Create a Transport Zone
Transport zones determine which hosts and by extension which virtual machines can use a particular segment (network). Hosts get added to transport zones. When a host is a member of a transport zone it can “see” all the segments that were created under that transport zone. A transport zone can span multiple clusters however, segments cannot span multiple transport zones.
(How-To) Configure Transport Node Profiles
Transport node profiles ensure a consistent, reliable deployment of transport nodes within your infrastructure. We will walk through the configuration of a transport node profile from start to finish.
(How-To) Prepare Host Transport Nodes (ESXi)
We are going to walk through the preparation of our ESXi hosts to become Transport Nodes. Once complete, we will be able to start applying NSX-T features and policies to your data center deployment.